i have dealt with SSL and browser security errors for years, and few messages confuse users as much as this one. when a browser displays www.xnxx.com sent an invalid response. ERR_SSL_PROTOCOL_ERROR, it looks technical, alarming, and final. many users assume the website is broken forever or that their device is infected. in reality, this error is a signal that something went wrong during the secure connection process between your browser and the website.
this article explains the error in full depth, without shortcuts or guesswork. i walk through what the SSL protocol is, why browsers block the connection, how local settings or networks contribute, and what practical steps resolve the issue. the focus is understanding, not quick hacks. by the end, you will know exactly what the error means and how to approach it logically.
this is a technical networking and browser security topic. the website name in the error message is incidental. the same principles apply to any site triggering ERR_SSL_PROTOCOL_ERROR.
What ERR_SSL_PROTOCOL_ERROR Really Means


SSL stands for Secure Sockets Layer, now technically replaced by TLS, Transport Layer Security. browsers still use the term SSL because it is widely recognized. when you visit a website using https, your browser attempts to establish a secure encrypted connection with the server.
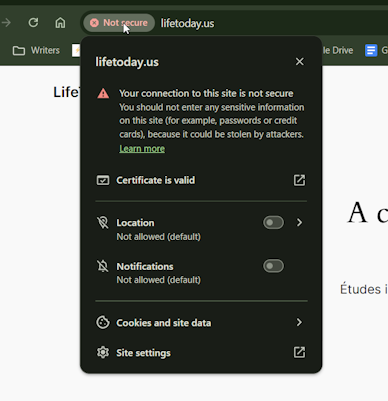
ERR_SSL_PROTOCOL_ERROR appears when that handshake fails. the browser and the server cannot agree on how to communicate securely. this failure happens before any page content loads, which is why the browser blocks access completely.
this is not a content error. it is not caused by the page itself failing to load. it is a security negotiation failure. browsers are strict here because insecure connections expose users to data interception and tampering.
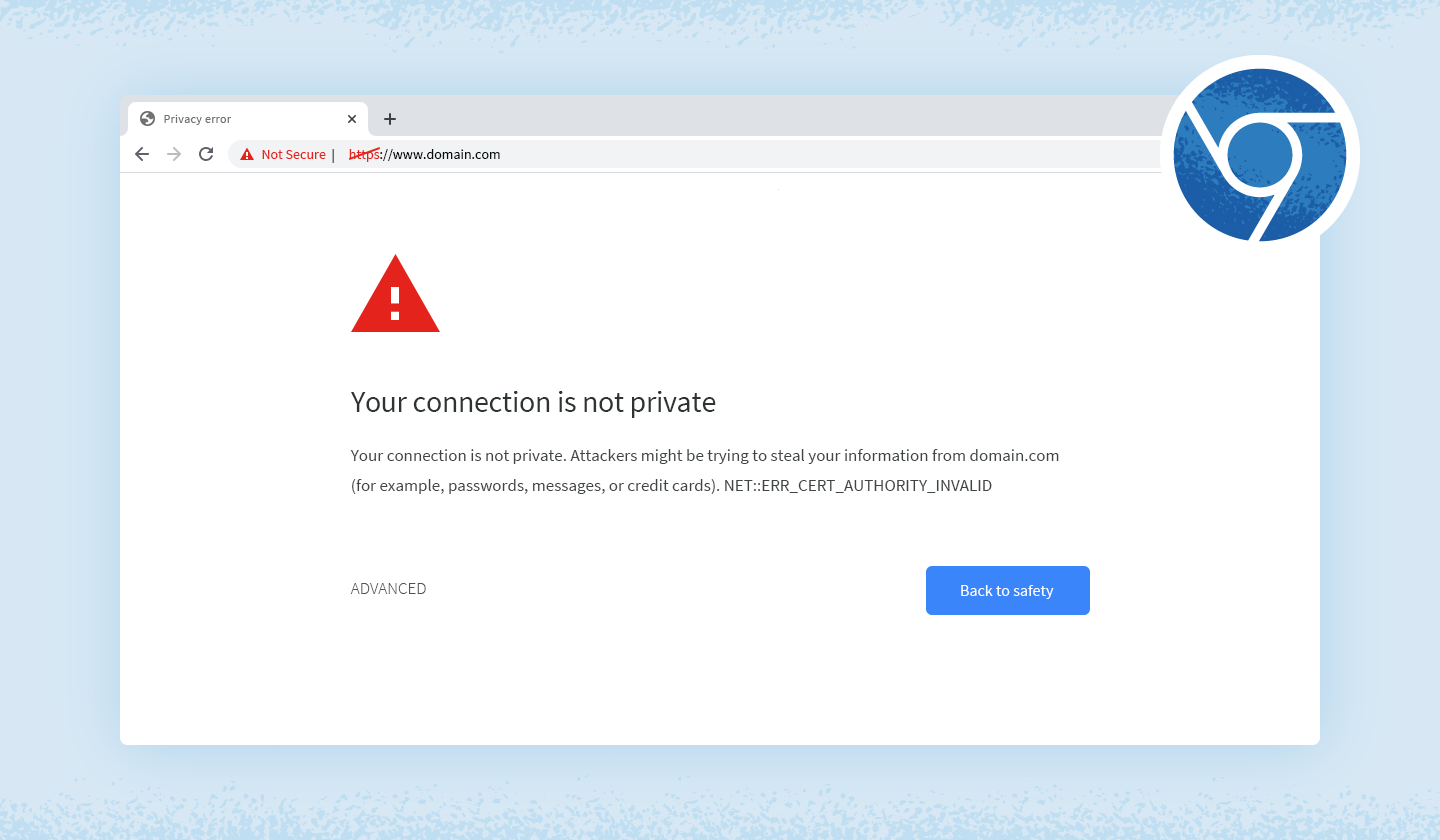
How the SSL Handshake Works
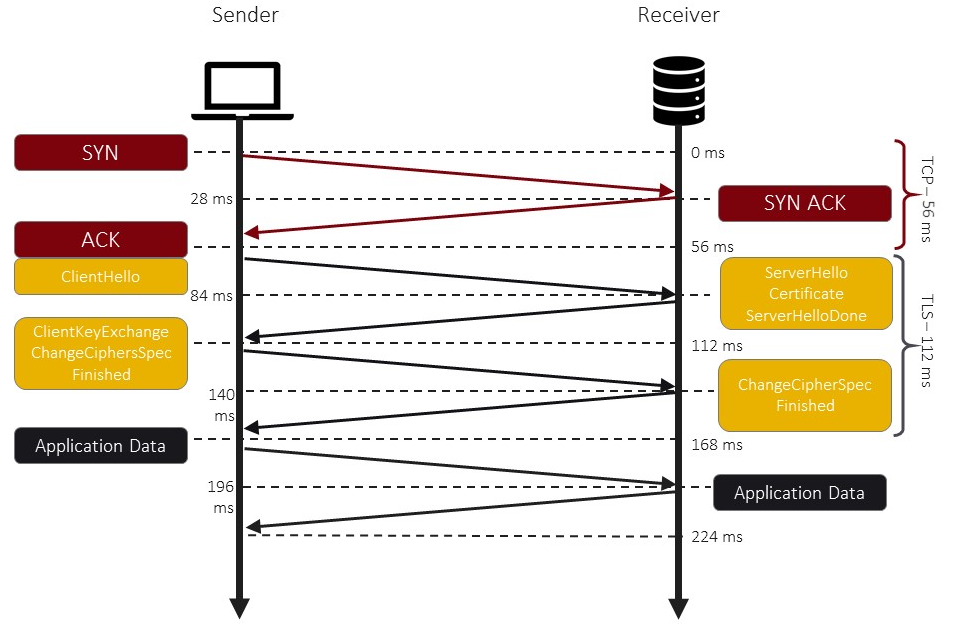
when you type a secure website address, several steps occur in milliseconds. your browser sends a request asking the server to identify itself and propose encryption methods. the server responds with its digital certificate and supported protocols.
the browser verifies the certificate, checks expiration dates, validates the issuing authority, and ensures protocol compatibility. only after this process succeeds does encrypted data exchange begin.
ERR_SSL_PROTOCOL_ERROR means the handshake stopped somewhere in this chain. either the certificate was rejected, the protocol version was unsupported, or the response from the server did not meet security expectations.
Why This Error Appears on Some Networks but Not Others


one of the most confusing aspects of this error is inconsistency. the site may open on mobile data but not on home Wi-Fi. this behavior strongly suggests network-level interference.
some internet service providers, corporate firewalls, and institutional networks inspect or filter encrypted traffic. when they interfere incorrectly, they can disrupt SSL handshakes.
in some regions, DNS filtering or traffic redirection modifies the connection before it reaches the destination server. the browser then receives an unexpected or malformed response, triggering ERR_SSL_PROTOCOL_ERROR.
this explains why switching networks often changes the outcome without changing anything on the device itself.
Browser Configuration as a Trigger
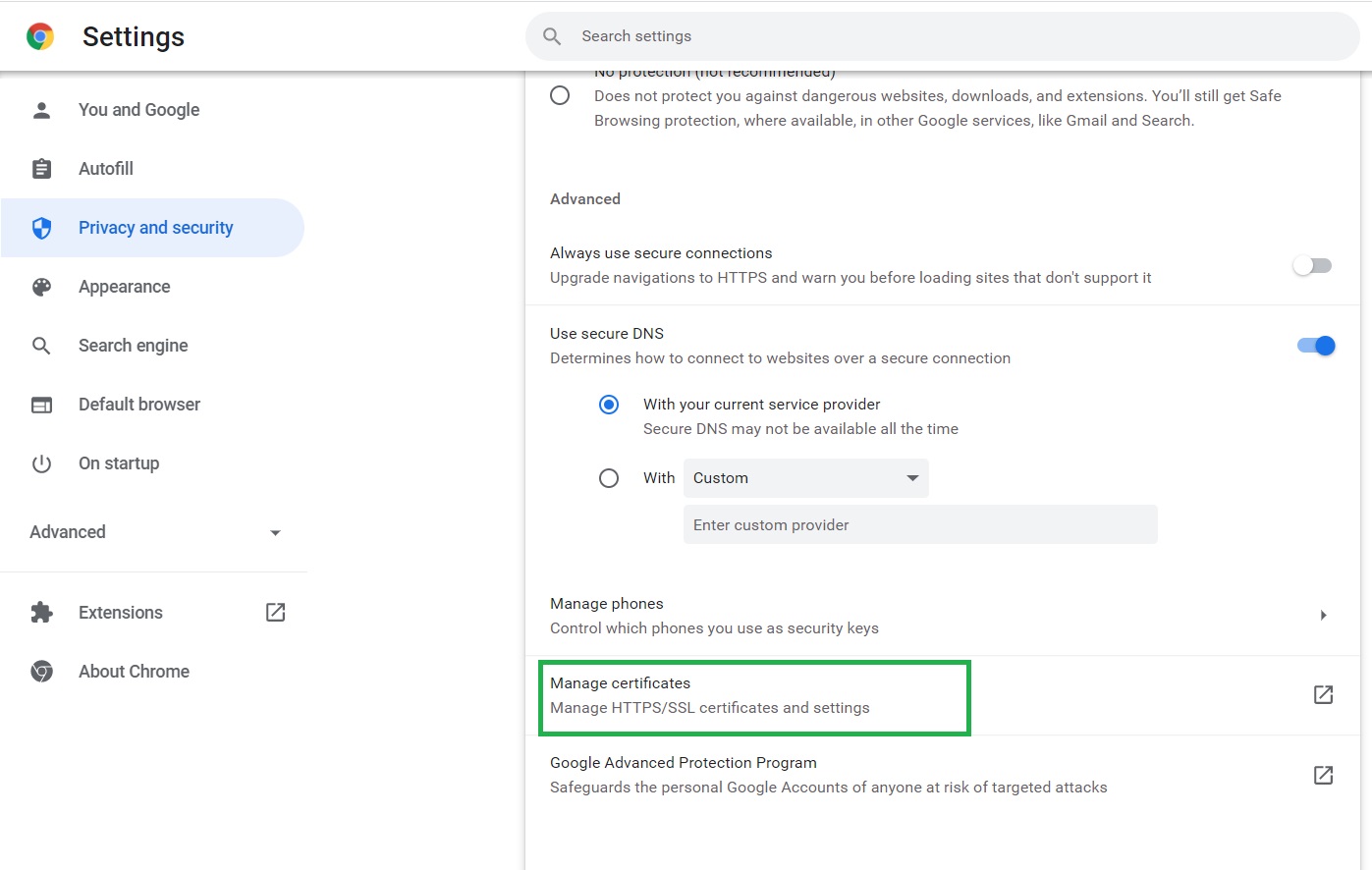

modern browsers maintain their own SSL state, caches, and security policies. corrupted SSL cache entries or outdated security settings can cause handshake failures.
browser extensions also play a role. privacy tools, VPN extensions, and traffic inspectors can intercept secure connections. if they fail to forward data correctly, the browser detects a protocol violation.
clearing SSL state, disabling extensions temporarily, or resetting browser settings often resolves these local configuration conflicts.
The Role of System Date and Time



this may sound trivial, but system time matters greatly for SSL. certificates are valid only within specific date ranges. if your device clock is incorrect, certificates may appear expired or not yet valid.
when that happens, browsers terminate the connection immediately. they treat invalid certificate timing as a security threat.
ensuring accurate date and time synchronization with internet time servers is one of the simplest and most overlooked fixes.
DNS Issues and SSL Protocol Errors
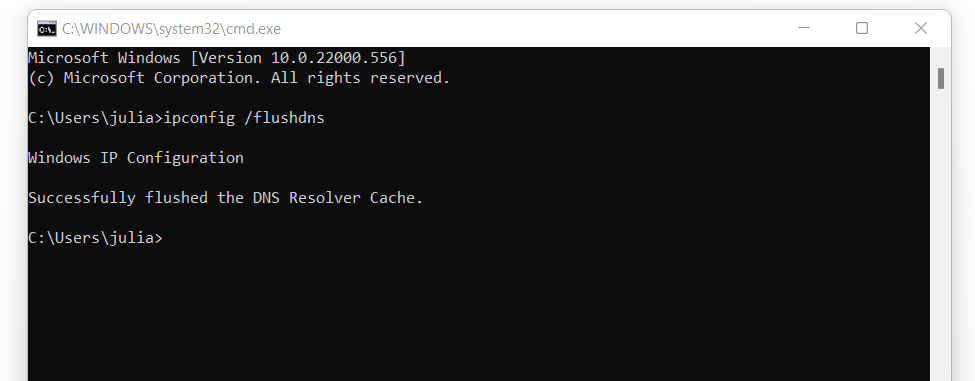
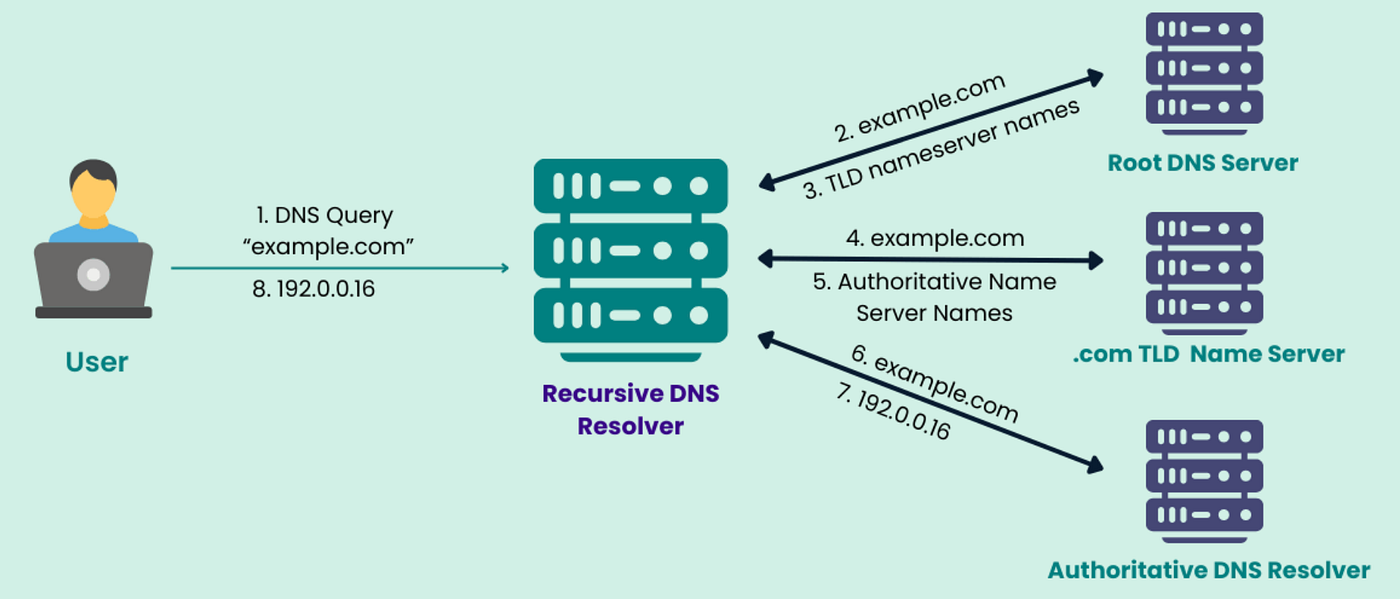
DNS translates domain names into IP addresses. if DNS records are outdated, manipulated, or blocked, your browser may connect to the wrong server.
connecting to an unintended server causes certificate mismatches. the server presents a certificate that does not match the domain name requested, leading to protocol errors.
changing DNS servers to reliable public options or flushing the DNS cache can resolve this class of issues.
Common DNS Options Comparison
| DNS Provider | Primary DNS | Secondary DNS |
|---|---|---|
| Google DNS | 8.8.8.8 | 8.8.4.4 |
| Cloudflare | 1.1.1.1 | 1.0.0.1 |
| OpenDNS | 208.67.222.222 | 208.67.220.220 |
When Antivirus or Security Software Causes the Problem

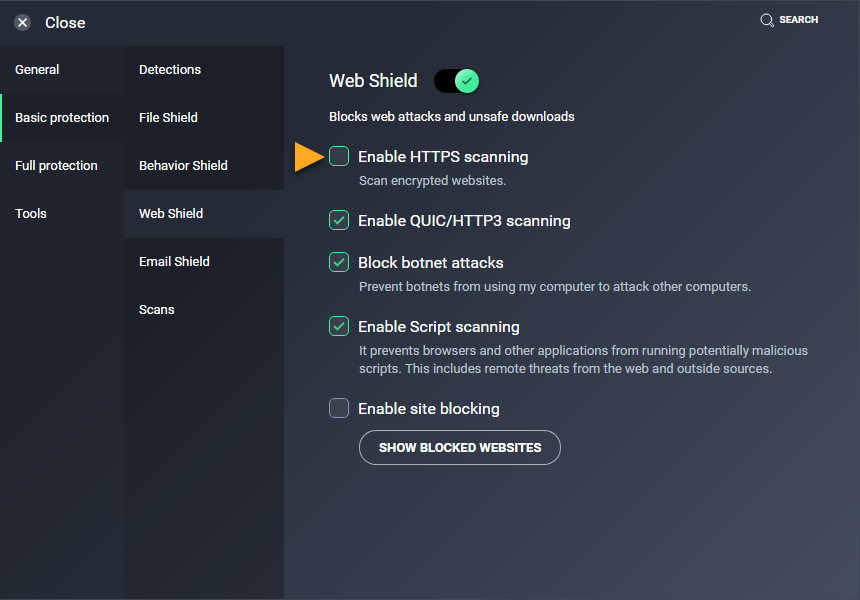

many antivirus programs scan encrypted traffic by installing local certificates and intercepting SSL connections. while intended for protection, this process can fail.
if the antivirus certificate is corrupted or outdated, the browser rejects the connection. this produces ERR_SSL_PROTOCOL_ERROR even though the destination server is valid.
temporarily disabling HTTPS scanning or updating the security software often restores normal behavior.
Server-Side Issues You Cannot Fix



sometimes the problem truly lies with the server. misconfigured SSL certificates, unsupported protocol versions, or incomplete certificate chains cause browsers to block access.
in these cases, nothing on the user side will permanently fix the error. the server owner must correct the configuration.
however, different browsers have different tolerance levels. one browser may load the site while another refuses, leading users to misinterpret the root cause.
Why Modern Browsers Are Less Forgiving


security standards evolve constantly. browsers update frequently to address new vulnerabilities. protocols and ciphers considered safe years ago are now blocked.
older servers that have not updated their SSL configurations may suddenly fail to load in newer browsers. this shift protects users but increases compatibility issues.
ERR_SSL_PROTOCOL_ERROR is often the visible result of these stricter enforcement policies.
Step-by-Step Logical Troubleshooting Process

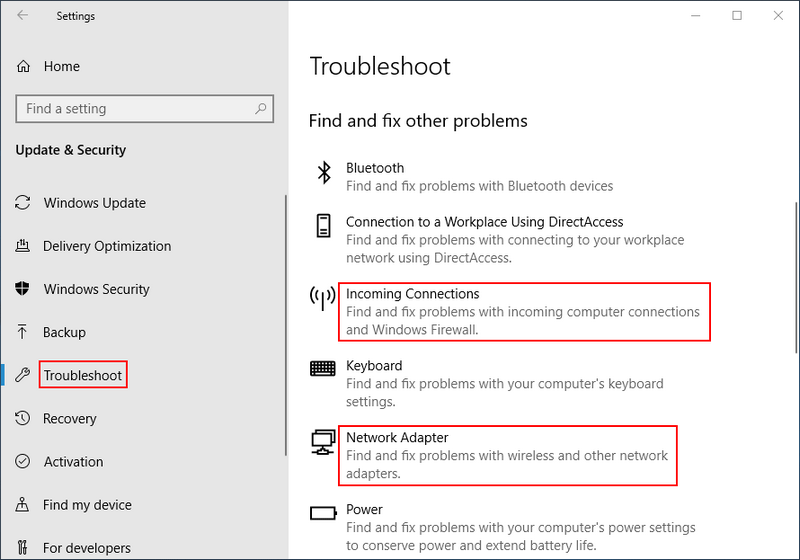
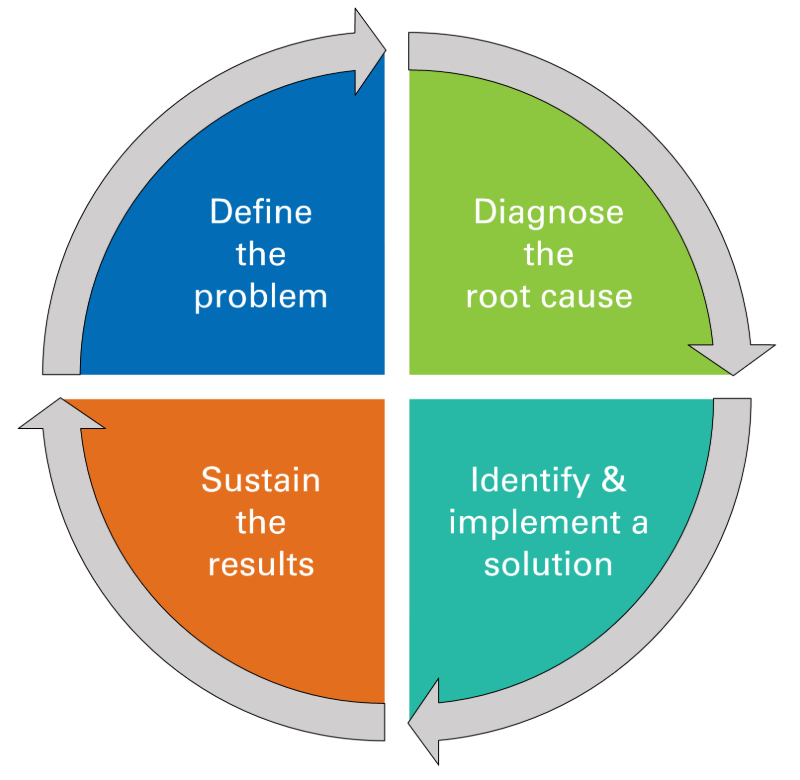
a systematic approach saves time. first, test the site on another network or device. second, check date and time settings. third, clear browser SSL state and cache.
fourth, disable extensions and antivirus HTTPS scanning temporarily. fifth, change DNS servers. if none of these steps work, the issue is likely server-side or network-level filtering beyond user control.
approaching the problem logically avoids unnecessary reinstallations or risky software downloads.
Mobile Browsers vs Desktop Browsers



mobile networks often route traffic differently than home broadband. mobile browsers may also use different certificate stores.
this explains why the same site loads on a phone but fails on a desktop browser. the difference is not the website but the connection path and security layers.
understanding this helps users diagnose network-based restrictions quickly.
Corporate, School, and Public Networks


many institutional networks block certain categories of websites using deep packet inspection. when this filtering interferes with SSL negotiation, browsers receive invalid responses.
the error message does not explicitly say the site is blocked. instead, it reports a protocol failure. this indirect behavior often confuses users.
in such environments, the restriction is intentional and cannot be bypassed without violating network policies.
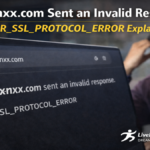
Is This Error Dangerous
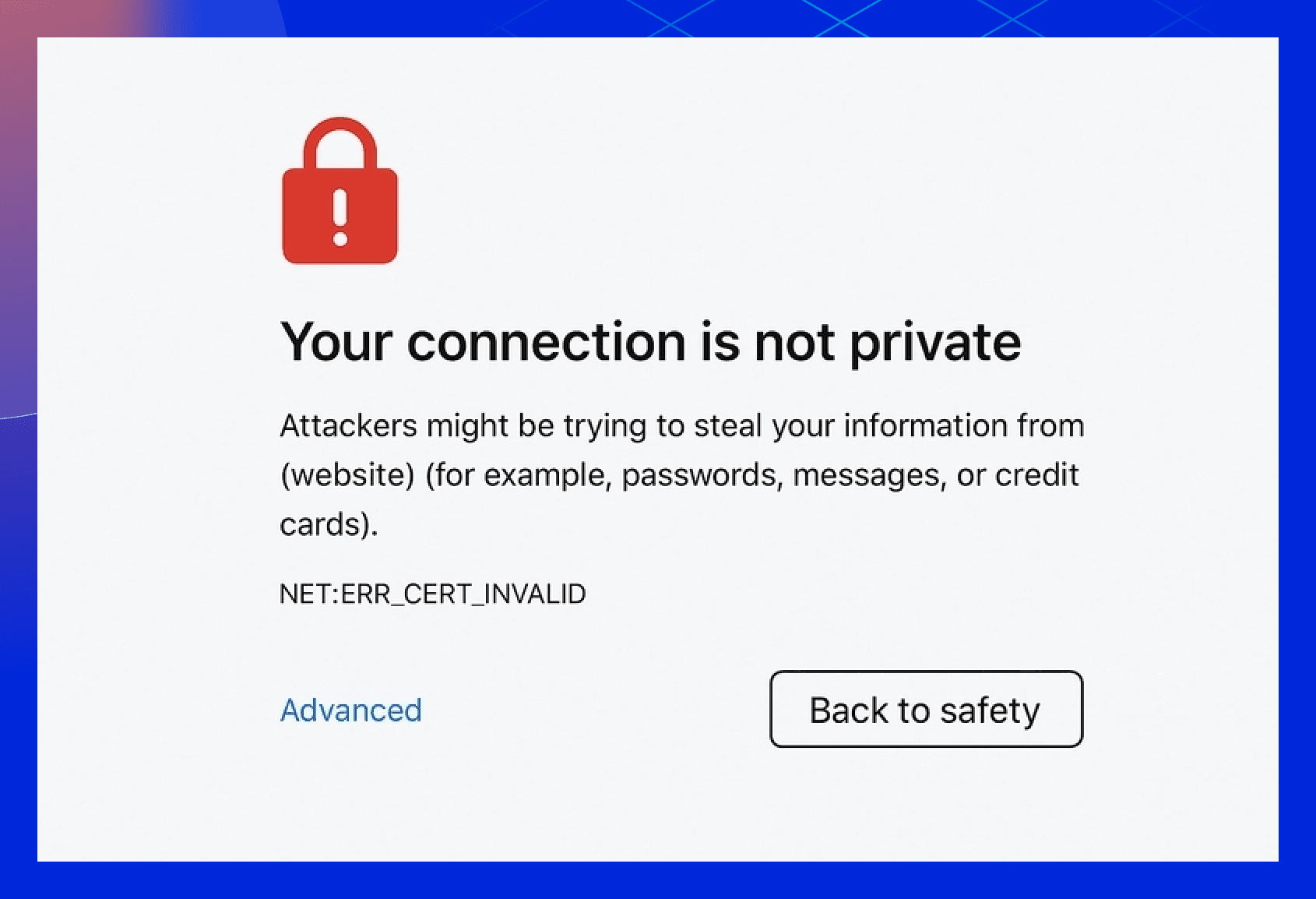

ERR_SSL_PROTOCOL_ERROR is a protective mechanism. it prevents data exposure. the error itself is not dangerous, but ignoring it through unsafe overrides can be.
browsers block access because they cannot guarantee connection integrity. attempting to bypass security warnings exposes users to potential interception or manipulation.
the safest approach is resolution, not circumvention.
Long-Term Fixes vs Temporary Workarounds


temporary fixes such as switching networks or browsers may restore access, but they do not address underlying causes.
long-term fixes involve updating systems, correcting DNS configurations, maintaining accurate time settings, and using reliable security software.
understanding the difference prevents recurring frustration.
Key Takeaways
- ERR_SSL_PROTOCOL_ERROR is a secure connection failure
- it occurs during the SSL or TLS handshake
- network interference is a common cause
- browser settings and extensions matter
- incorrect system time breaks certificates
- some server issues are outside user control
Conclusion
www.xnxx.com sent an invalid response. ERR_SSL_PROTOCOL_ERROR looks intimidating, but it is fundamentally a communication breakdown between browser and server security layers. the error protects users from insecure connections rather than indicating device failure.
by understanding how SSL works and what disrupts it, users can troubleshoot calmly and effectively. most causes are environmental, not permanent. others reflect intentional network restrictions or outdated server configurations.
the real value lies in recognizing that this error is informational, not catastrophic. when approached logically, it becomes manageable rather than mysterious.
Read: Best AI Attractive Test: Analyze Your Face Attractiveness
FAQs
What does ERR_SSL_PROTOCOL_ERROR mean
it means the browser failed to establish a secure encrypted connection with the server.
Can clearing browser cache fix this error
yes, corrupted SSL cache or cookies can cause handshake failures.
Why does the site work on mobile data but not Wi-Fi
network filtering or DNS differences often cause this behavior.
Is my computer infected if I see this error
no, the error is a security protection, not a malware warning.
Can I safely bypass this SSL error
no, bypassing SSL warnings risks exposing data and is not recommended.